Facebook is undoubtedly the king of social networking and with the
majority of its users logging in multiple times in a day, to either
check out their friends updates or post their own status. With these
usage factors in mind, its important to make use of some of the tricks
to better your usage and speed up your time Facebook so that you get
more time for the life outside Facebook.

So
here are some of the cool tricks that will help you in managing your
account more easily and also some cool tricks to show off your geeky
side.Enjoy.:)
1 How to Download entire Facebook Photo Albums
Tired
of copying individual photos of your friends album that he/she shared
of your last vacation?..Well here is a time saving and a faster solution
called
FacePAD,available for Mozilla Firefox browser, allows you to download the entire Facebook album with a single click.

2.How to Schedule your Facebook Status Updates and Messages
What
if you wont be logging into Facebook for a few days as you are going
on a vacation or something and you need to post some updates or send
messages on a particular day, well
sendible makes it easy to schedule your status updates and messages.Although you can use a simpler alternative called
LaterBro which is less time consuming than the Sendible.

3 How to Hide Online Status from Certain people in Chat
This
is a basic feature available in Facebook, but not many of them use this
as they still don’t know this.Create separate lists of friends and set
the status for each list separately.

4 How to Friend a person and hide this update
This
is an important and useful trick that can be used to friend a person
without letting his/her friends getting the update( like your ex ‘s
sister or someone..:P)…Here is a quick guide for the trick from
Makeuseof Tutorial.

5 How to add cool symbols to your Facebook Status
You might have seen people posting weird symbols on their status, well you can do that too.Head over to
this link or
here to find out the various alt codes to use in your status.For more Check out
Hongkiat
6 How to show your Facebook status on your WordPress blog
Here is a plugin called
StatusPress that lets you view the status updates on a widget in your WordPress blog.Install it and you are good to go.
7 How to turn your Status updates into a cool 3D Word Cloud
This trick requires a Facebook application called
Status Analyzer 3D
which gets you a list of status updates and turns them into colorful
animated word cloud which you can then share with your friends.

8 How to Get Status Updates from Anyone around the World
This is kind of like a trick to exploit the privacy set by the users. Head over to
YourOpenBook and you can search anyone’s status by selecting the gender and the keyword or you can even browse the recent searches made.

9 How to Update Your Facebook Status From Firefox Browser
You
can post your Facebook status directly from your Firefox browser using 2
Firefox plugins.Well there seems to thousands of plugins for everything
for Firefox and here are the 2 plugins
FireStatus or a toolbar
Facebook Toolbar .
10 How to Automatically Poke Back your friends who poked you
If you don’t have enough time to poke back every time someone pokes you then try out this Grease Monkey Script called
Facebook AutoPoke
11 How to Update your Facebook Status Directly from Gmail
Here is a great gadget called
Facebook Gadget from iGoogle that lets you post updates directly from your Gmail.
12 How to Access Gmail Data from Facebook
This is a awesome feature if you often log into Facebook than your Gmail account.Check out a Facebook Application called
Fmail that lets you browse your Gmail in Facebook.
13 How to Get Facebook in your Desktop
If
you like to stay on your desktop to browse Facebook rather go to your
time consuming web browser to start up and load all the tabs and
stuff.Check out these tools for easier Facebook access on your desktop
using these Facebook desktop clients
Facebook Desktop,
Scrapboy ,
Seesmic Desktop,
Facebook Sidebar Gadget ,
Facebooker,
Facebook AIR application FaceDesk,
Xobni,
FBTrayNotify.
14 How to access Facebook Chat on your Desktop
If you just want to chat with your online facebook friends from your desktop, check out the popular tools like
Digsby,or
Gabtastik, or other options like
adium.

15 How to Create a photo Collage using all your facebook friends pictures.
Want to create a beautiful collage of all your Facebook friends pictures, well head over to Facebook application called
Photo Collage, you can then share the result with your friends and have fun.
16 Post Upside Down Status Updates on your Wall
If you have seen friends posting upside down status updates and even you would like to try em, check out this tool called
FlipText which provides you with the upside down text to post on your wall.

17 Get your Facebook Profile as Pirates Page
Change
your Facebook Profile language settings to English(Pirate) in the
language settings.You will notice hilarious pirate language
transformations like , comment -> blabber t’yer mates, whats on your
mind -> what be troublin’ ye? and a whole lot more. I Really loved
this feature and i still use it cause its a whole lot fun and makes
Facebook much more exiting.

18 How to Upload and Share Flickr Photos on Facebook
This is a great tool if you have your albums uploaded in Flickr and wanted to upload them into Facebook. The plugin is called
Flickr2Facebook that gets you this job done easily.
19 Update Your Facebook Pages without Using Facebook
There
are 2 major services that offer these features Hellotxt and Ping Fm.
Although both the services are closely competitive , hellotxt has been
the older player than ping Fm and is more convenient to set up and use
than ping fm.


20 How to Download Videos from Facebook
Facebook
has a large vast collection of shared videos and if you want to
download them into your hard disk, then use a online tool called
DownFacebook.
21 How to Show Only Selected Profile Pictures on your Friends list in your Facebook Profile
Well
if you are trying to find the trick to edit your friends list pictures
to show up only your particular friends then here is the trick. Click on
the edit button(looks like a pencil) above your friends box,in the
“Always show these friends”, select only those friends that you would
like to see in your friends list by others.And you are good to go.

22 How to Post your Blog Posts automatically on your Facebook Page or your wall
There are 2 most widely used plugins or tools available to automatically onto your Facebook wall.
If you are a WordPress user then check out a plugin called
WordBook that lets you automatically post on your wall.
For other blogging platforms, check out another popular tool or a Facebook plugin called
Networked Blogs which offers you this feature.An alternative to Networked blogs is
RSS Graffiti .
23 How to View Facebook as in Twitter
If
you are a big fan of twitter or you either like to have fun with your
Facebook interface, then check out this cool hack to change your
Facebook into twitter style using a Greasemonkey script from userscripts
here.
24 How to Import and add Facebook friends to twitter
Here
is a great app that lets you follow the right people who are in your
Facebook friends list and follow the on twitter using the Facebook App
called
Friend Lynx.
25 How to Check your very status updates stats or find your very old status
Well the app called
Status Statistics
that lets you see all your status updates stats and generate a list of
your updates along with the graph of your posting times in a day and
particular days in a week. So if you had to find your old status update ,
then this can help you in saving time in going through your history on
your wall.
26 How to Update your Facebook Status from Twitter (or update Both simultaneously)
This
is another cool app that will help the everyday twitter users to update
their Facebook walls at the same time as their tweets.Check out the
Twitter App for Facebook that will set your status updates same time as you tweet once the app is in sync with your twitter account.
27 How to do the Worst Profile Trick
This
is a simple trick to post a profile id on your wall and when your
friends click on it will take them to their own profile..Check this out,
here is the trick..Post your status “Worst Profile ever
http://facebook.com/profile.php?=73322363″ and its done.

28 How to Access Facebook From Microsoft Outlook
Facebook
seems to be accessible from everywhere, and here is a way to access
using the Microsoft Outlook. This is often useful in cases where
Facebook is banned in college networks , so try out this plugin called
FBLook to access Facebook through Microsoft Outlook.
29 Keyboard Shortcuts to use in Facebook
This
shortcuts are less known as people prefer to use their mouse rather
than go with these shortcut keys..But just to let you know here they are
Internet Explorer :
Alt-1 – Enter goes to Home page;
Alt-2- Enter goes to your profile;
Alt-3- Enter lets you view Friend requests;
Alt-M- Enter starts a new message;
Alt-Enter places your cursor in Facebook’s Search box.
Firefox-Same keys but replace Alt with “Alt+ Shift”
30 How to remove Facebook Advertisements
If
you don’t want those Facebook ads popping up on your Facebook walls and
pages, then use this Grease Monkey Script from UserScripts to clean up
those messy ads –>
Script link. Another alternative for Firefox users is to use the Firefox plugin called
AdBlock Plus

Share your tips or tricks that you would like to share with us and do let us know by your comments..Cheers..:)





































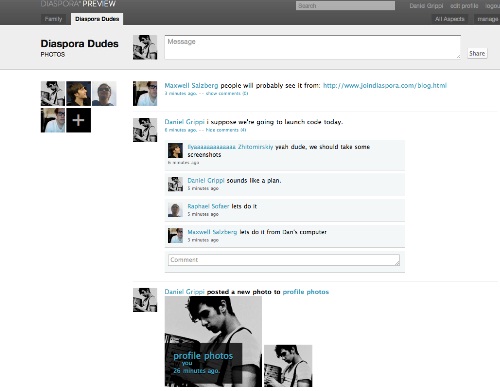 For those of you who still haven’t registered for Google+, how about checking out Diaspora for the time being until that time. Diaspora allows invites of about 10 per account, but it is possible to send more invites. So follow these steps to land yourself a invite to the most popular open social networking site available on the internet.
For those of you who still haven’t registered for Google+, how about checking out Diaspora for the time being until that time. Diaspora allows invites of about 10 per account, but it is possible to send more invites. So follow these steps to land yourself a invite to the most popular open social networking site available on the internet.















