| 1 |  | Wireless Lan Security Megaprimer Part 1: Getting Started |
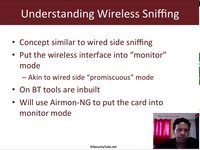
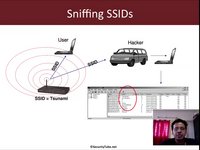
| 2 |  | Wireless Lan Security Megaprimer Part 2: Bands, Channels And Sniffing |
| 3 |  | Wireless Lan Security Megaprimer Part 3: Pwning Beacon Frames |
| 4 |  | Wireless Lan Security Megaprimer Part 4: Dissecting Ap-Client Connections |
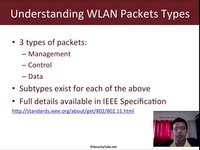
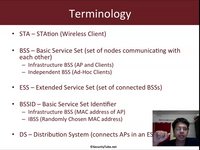
| 5 | 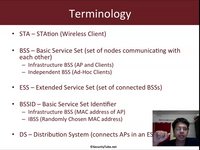 | Wireless Lan Security Megaprimer Part 5:Dissecting Wlan Headers |
| 6 | 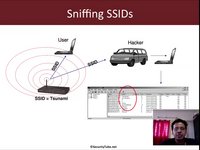 | Wireless Lan Security Megaprimer Part 6: Pwning Hidden Ssids |
| 7 |  | Wireless Lan Security Megaprimer Part 7: Laughing Off Mac Filters |
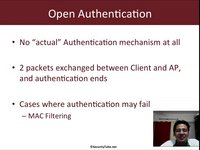
| 8 | 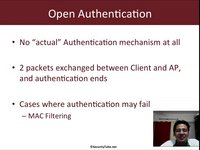 | Wireless Lan Security Megaprimer Part 8: Hacking Wlan Authentication |
| 9 | 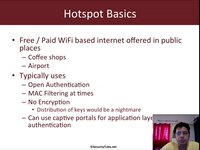 | Wireless Lan Security Megaprimer Part 9: Hotspot Attacks |
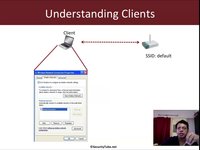
| 10 |  | Wireless Lan Security Megaprimer Part 10: Hacking Isolated Clients |
| 11 | 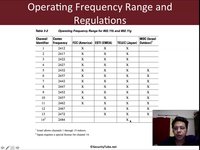 | Wireless Lan Security Megaprimer Part 11:Alfa Card Kung-Fu |
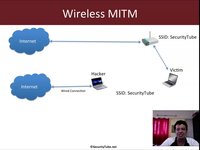
| 12 | 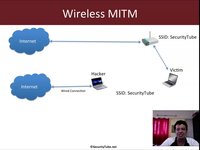 | Wireless Lan Security Megaprimer Part 12: Man-In-The-Middle Attack |
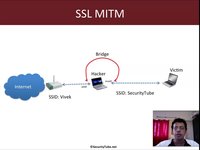
| 13 |  | Ssl Mitm Attack Over Wireless |
| 14 |  | Ssl Mitm Attack Over Wireless Demo |
| 15 | 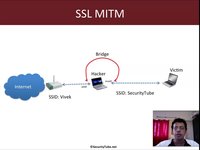 | Wireless Lan Security Megaprimer Part 13 : Ssl Man-In-The-Middle Attacks |
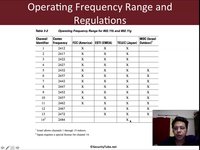
| 16 |  | Custom Wireless Regulation Database |
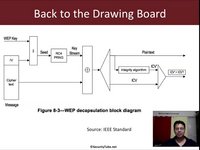
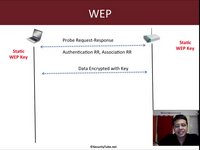
| 17 | 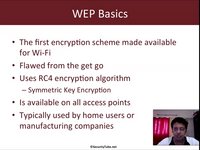 | Wireless Lan Security Megaprimer Part 14: Wep In-Depth |
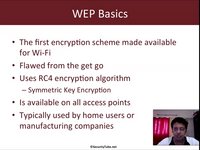
| 18 | 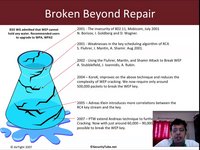 | Wireless Lan Security Megaprimer Part 15: Wep Cracking |
| 19 | 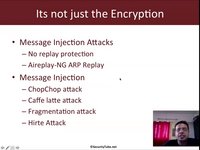 | Wireless Lan Security Megaprimer Part 16: Caffe Latte Attack Basics |
| 20 | 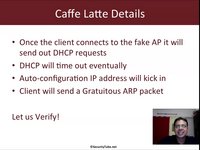 | Wireless Lan Security Megaprimer Part 17: Caffe Latte Attack Demo |
| 21 |  | Caffe Latte Attack On The Iphone |
| 22 |  | Wireless Lan Security Megaprimer Part 18: Korek's Chopchop Attack |
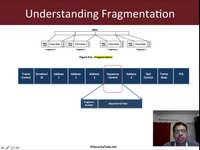
| 23 | 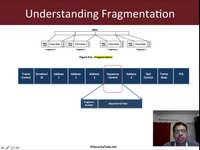 | Wireless Lan Security Megaprimer Part 19: Fragmentation And Hirte Attack |
| 24 |  | Wireless Lan Security Megaprimer Part 20: Understanding Wpa/Wpa2 |
| 25 |  | Wi-Fi Challenge 1 (Level Easy) : There Is No Patch For Stupidity! |
| 26 | 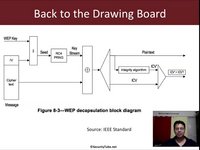 | Wi-Fi Challenge 1 Solution : There Is No Patch For Stupidity! |
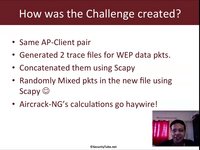
| 27 |  | Wi-Fi Challenge 2 (Level - Intermediate) : Know Thy Packets |
| 28 | 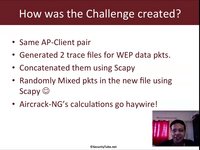 | Wi-Fi Challenge 2 Solution : Know Thy Packets |
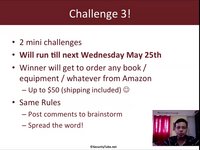
| 29 |  | Wi-Fi Challenge 3 (Level Advanced): Never Underestimate Your Enemy! |
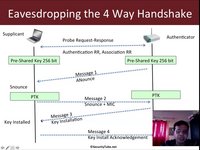
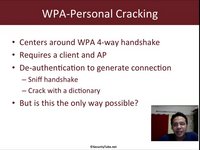
| 30 | 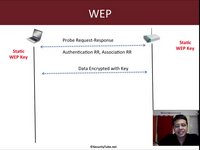 | Wireless Lan Security Megaprimer Part 22: Wpa-Psk |
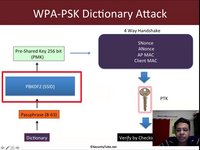
| 31 | 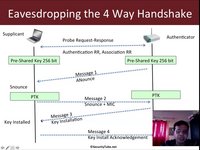 | Wireless Lan Security Megaprimer Part 22: Wpa-Psk Cracking |
| 32 |  | Wireless Lan Security Megaprimer Part 23: Wpa2-Psk Cracking |
| 33 | 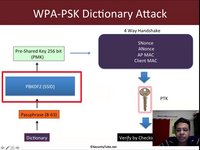 | Wireless Lan Security Megaprimer Part 24: Speeding Up Wpa/Wpa2 Psk Cracking |
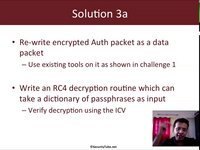
| 34 | 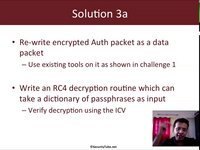 | Wi-Fi Challenge 3 Solution: Never Underestimate Your Enemy! |
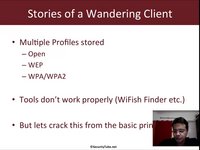
| 35 | 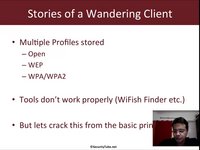 | Wlan Security Megaprimer Part 25: Mood Swings Of A Wandering Client |
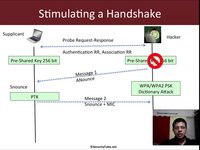
| 36 | 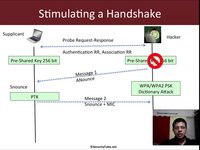 | Wlan Security Megaprimer Part 26: Cracking Wpa/Wpa2-Psk With Just The Client |
| 37 |  | Wlan Security Megaprimer: Questions And Answers |
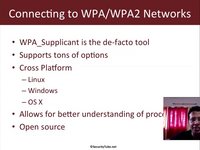
| 38 | 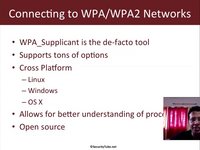 | Wireless Lan Security Megaprimer Part 28: Wpa_Supplicant |
| 39 | 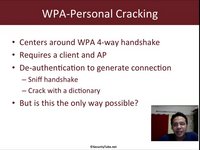 | Wireless Lan Security Megaprimer Challenge 4: Crack Wpa-Personal With Only Ap |
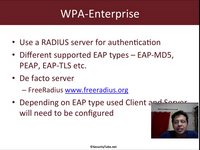
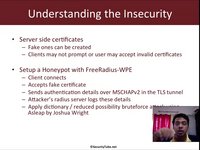
| 40 | 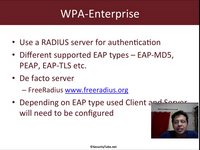 | Wireless Lan Security Megaprimer 29: Setting Up Freeradius-Wpe On Backtrack |
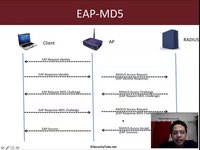
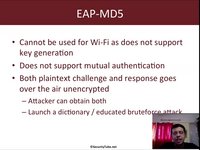
| 41 | 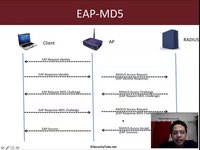 | Wireless Lan Security Megaprimer 30: Eap-Md5 Basics And Demo |
| 42 | 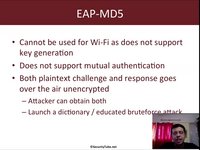 | Wireless Lan Security Megaprimer 31: Cracking Eap-Md5 With Eapmd5Pass And Eapmd5Crack |
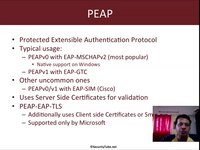
| 43 | 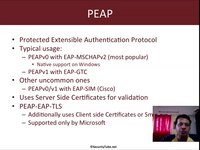 | Wireless Lan Security Megaprimer 32: Eap Types And Peap Demo |
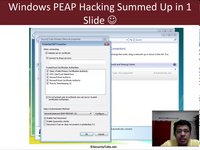
| 44 | 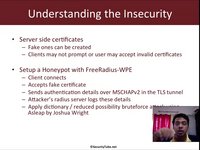 | Wireless Lan Security Megaprimer 33: Cracking Peap |
| 45 | 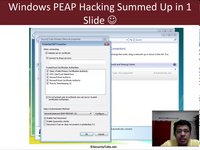 | Wireless Lan Security Megaprimer 34: Cracking Peap In A Windows Network |
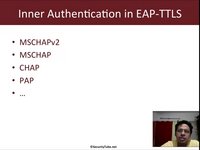
| 46 | 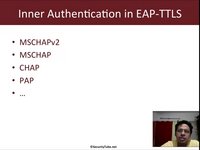 | Wireless Lan Security Megaprimer 35: Cracking Eap-Ttls |
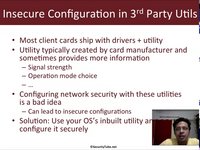
| 47 |  | Wireless Lan Security Megaprimer 36: Insecurity In 3Rd Party Wi-Fi Utilities |
| 48 |  | Wireless Lan Security Megaprimer : Conclusion And The Road Ahead |
| 49 |  | Windows Wireless Kung-Fu (Swse Addendum 1) |
| 50 |  | Creating Wireless Backdoors (Swse Addendum 2) |
| 51 |  | Malware, Metasploit And The Hosted Network (Swse Addendum 3) |
| 52 |  | Securitytube Certified Wi-Fi Security Expert (Swse) Student Portal |